
Sorry, your browser is not compatible with this application. Please use the latest version of Google Chrome, Mozilla Firefox, Microsoft Edge or Safari.
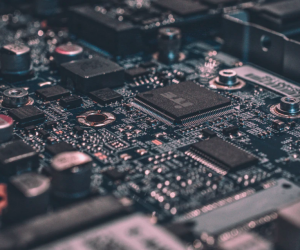
Validating the Integrity of Computing Devices
Organizations are increasingly at risk of cyber supply chain compromise, whether intentional or unintentional. Cyber supply chain risks include counterfeiting, unauthorized production, tampering, theft, and insertion of unexpected software and hardware. Managing these risks requires ensuring the integrity of the cyber supply chain and its products and services.
This project demonstrates how organizations can verify that the internal components of the computing devices they acquire, whether laptops or servers, are genuine and have not been tampered with. This NIST Cybersecurity Practice Guide describes the work performed to build and test the full solution.
| Format: |
|
| Topics: | |
| Website: | Visit Publisher Website |
| Publisher: | National Institute of Standards and Technology (NIST) |
| Published: | December 9, 2022 |
| License: | Public Domain |
Featured Content

Contact Publisher


Claim Content





