
Sorry, your browser is not compatible with this application. Please use the latest version of Google Chrome, Mozilla Firefox, Microsoft Edge or Safari.
Establishing a Zero Trust Model in IoT Environments
In February of 2023, a United States healthcare provider disclosed that malicious actors breached their network, exfiltrated clinical images and protected health information (PHI) about cancer patients, then published it in the public domain. The attackers demanded ransom, but the provider refused to pay. The attackers then published the data on the dark web in retaliation. An organization with a noble mission and vital role in our society suffered disruption, the loss of data and reputation and likely monetary damages.
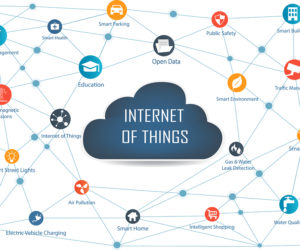
However, this story is unique in at least one respect: the hackers exploited the convergence of Internet of Things (IoT) and information technology (IT) systems, a convergence that is also growing exponentially, not just in healthcare provision but across all industries and sectors. In this case, a medical device (IoT) captured patient images for radiation oncology treatment and transferred them to a networked computer system (IT).
| Format: |
|
| Topics: | |
| Website: | Visit Publisher Website |
| Publisher: | Verizon |
| Published: | August 11, 2023 |
| License: | Copyrighted |
| Copyright: | © 2023 Verizon. |
Featured Content

Contact Publisher


Claim Content





