
Sorry, your browser is not compatible with this application. Please use the latest version of Google Chrome, Mozilla Firefox, Microsoft Edge or Safari.
Find Government White Papers & Related Content

Browse over one thousand military and government white papers, eBooks, case studies, infographics, and data sheets.
Search by topic, agency, keyword, and more to find government-related content that explores the challenges, trends and solutions available to government organizations. Or, simply start browsing the latest content below. Government white papers include research findings on a wide range of topics such as blockchain, big data, cybersecurity, defense, and emergency management, among others.
Your free membership allows you to save your favorite content as well as save your searches to keep you notified when new, relevant content is posted.

Featured Content

Technical and Legal Criteria for Assessing Cloud...
Concerns about trusting cloud services have existed since their creation. Growing geopolitical tension, coupled with the cloud’s pivotal roles in data privacy and cyber and national security, are prompting policymakers…
Learn More

DevSecOps: Continuous Authorization Implementation...
The exigencies of today demand the agility to respond to changing mission needs by delivering capabilities more rapidly than with traditional Department of Defense (DoD) processes. To enable such a…
Learn More


China and Medical AI: Implications of Big Biodata...
Medical artificial intelligence, which depends on large repositories of biological data, can improve public health and contribute to the growing global bioeconomy. Countries that strategically prioritize medical AI could benefit…
Learn More


China, Biotechnology, and BGI
As the U.S. government considers banning genomics companies from China, it opens a broader question about how the United States and other market economies should deal with China’s “national champions.”…
Learn More


Zero Trust Policy Engine: An In-Depth Analysis
Today’s organizations face the task of securing a digital core beyond traditional network boundaries. Coupled with the rise in data volumes and the sophistication of cyberattacks, the IT landscape calls…
Learn More


Absolute Secure Access with ZTNA Policy
The Absolute Secure Access platform is available as a cloud-hosted, SaaS solution that allows customers to harness Absolute’s Zero Trust Network access, experience monitoring and enterprise next gen VPN capabilities…
Learn More


2024 Absolute Security Cyber Resilience Index...
The 2024 Absolute Security Cyber Resilience Index Report identifies key enterprise security risk factors that cyber resilience technologies mitigate. Other security and risk professionals learn how to determine whether identified…
Learn More


NextLabs’ Solution for the Cybersecurity Maturity...
The Cybersecurity Maturity Model Certification (CMMC) is a framework developed by the U.S. Department of Defense (DoD) to enhance the cybersecurity posture of organizations in the Defense Industrial Base (DIB),…
Learn More

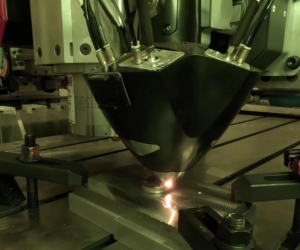
Resilient Advanced Manufacturing: Deployable Metal...
The evolving landscape of modern warfare and industrial operations has placed a premium on dependable and efficient manufacturing solutions. Snowbird Technologies meets these challenges with a visionary approach, spearheading a…
Learn More


Harnessing Next-Generation AI Solutions for...
The introduction of generative AI into the public domain has brought both significant opportunities and challenges to national security. While panelists are encouraged by the positive outcomes of recent AI…
Learn More


How to Enable Secure Mobility for Fixed Location...
The Future of Secure Work Base Paper outlines how the US Government (USG) has acknowledged the utility of mobile devices across environments. However, agencies that use sensitive or classified information…
Learn More


Cybersecurity: Implementation of Executive Order...
Federal agencies are dependent on IT systems and electronic data to carry out operations and to process, maintain, and report essential information. Virtually all federal operations are supported by computer…
Learn More


Explore the Universe with the First E-Book from...
Fermi provides a unique view of the universe and allows us to study some of its most curious phenomena. Fermi’s position in low-Earth orbit enables it to detect thousands of…
Learn More


Lookout Mobile Endpoint Security Solution Brief
Traditional cybersecurity strategies have long been focused on protecting your fixed endpoints such as servers, laptops and desktops from cyberthreats. However, your security requirements have grown organically over time. The…
Learn More


How to Get Started Modernizing Government Legacy...
Dealing with legacy code is a routine occurrence, yet the unknowns within the code pose significant risks. When the time comes to refresh or update technology, modernizing legacy systems can…
Learn More

